在 CentOS 8|RHEL 8|AlmaLinux 8 上安装 Wazuh 服务器 |
本文将介绍如何在 CentOS 8|RHEL 8|AlmaLinux 8 上安装 Wazuh 服务器。 Wazuh 服务器是一个使用 Elastic stack (ELK) 的免费开源安全监控工具。它用于监视应用程序和操作系统级别的安全事件。因此,您可以获得有关威胁检测、事件响应和完整性监控的信息。在本教程中,我们将在单节点 CentOS/RHEL/Rocky Linux 主机上部署 Wazuh,并在同一主机上安装 ELK。
您可以将 Wazuh 用于以下应用程序:
- 安全分析
- 日志分析
- 漏洞检测
- 集装箱安全
- 云安全
以下步骤将指导我们如何在 CentOS 8|RHEL 8|AlmaLinux 8 实例上设置 Wazuh 服务器。我们将考虑自动和手动安装方法。
硬件要求
此类部署的最低要求是:
- 4 GB 内存
- 2个CPU核心
- 64 位操作系统
推荐的有:
- 16 GB 内存
- 8个CPU核心
方法1:在CentOS 8|RHEL 8|AlmaLinux 8上无人值守安装Wazuh服务器
CentOS 8|RHEL 8|AlmaLinux 8 上 Wazuh 服务器最快的安装方法是使用提供的 bash 脚本。您需要首先将脚本下载到您的 Linux 计算机上。
cd ~/
curl -so wazuh-installation.sh https://packages.wazuh.com/resources/4.2/open-distro/unattended-installation/unattended-installation.sh下载脚本后,运行它以在 CentOS 8|RHEL 8|AlmaLinux 8 上安装 Wazuh 服务器:
sudo bash ./wazuh-installation.sh自动安装过程应立即开始。
03/01/2022 07:21:43 INFO: Installing all necessary utilities for the installation...
03/01/2022 07:22:44 INFO: Done
03/01/2022 07:22:44 INFO: Adding the Wazuh repository...
03/01/2022 07:22:49 INFO: Done
03/01/2022 07:22:49 INFO: Installing the Wazuh manager...
03/01/2022 07:23:52 INFO: Done
03/01/2022 07:24:10 INFO: Wazuh-manager started
03/01/2022 07:24:10 INFO: Installing Open Distro for Elasticsearch...
03/01/2022 07:24:41 INFO: Done
03/01/2022 07:24:41 INFO: Configuring Elasticsearch...
03/01/2022 07:25:14 INFO: Configuration file found. Creating certificates...
03/01/2022 07:25:14 INFO: Creating the Elasticsearch certificates...
03/01/2022 07:25:14 INFO: Creating Wazuh server certificates...
03/01/2022 07:25:14 INFO: Creating Kibana certificate...
03/01/2022 07:25:14 INFO: Certificates creation finished. They can be found in ~/certs.
03/01/2022 07:25:14 INFO: Certificates created
03/01/2022 07:26:12 INFO: Elasticsearch started
03/01/2022 07:26:12 INFO: Initializing Elasticsearch...
03/01/2022 07:26:31 INFO: Done
03/01/2022 07:26:31 INFO: Installing Filebeat...
03/01/2022 07:26:57 INFO: Filebeat started
03/01/2022 07:26:57 INFO: Done
03/01/2022 07:26:57 INFO: Installing Open Distro for Kibana...
03/01/2022 07:28:17 INFO: Kibana started
03/01/2022 07:28:17 INFO: Done
03/01/2022 07:28:23 INFO: Generating random passwords
03/01/2022 07:28:23 INFO: Done
03/01/2022 07:28:23 INFO: Creating backup...
03/01/2022 07:28:37 INFO: Backup created
03/01/2022 07:28:37 INFO: Generating hashes
03/01/2022 07:28:43 INFO: Hashes generated
03/01/2022 07:28:44 INFO: Filebeat started
03/01/2022 07:28:44 INFO: Kibana started
03/01/2022 07:28:44 INFO: Loading changes...保存在 CentOS 8|RHEL 8|AlmaLinux 8 上成功安装 Wazuh 服务器后打印的登录详细信息。
03/01/2022 07:28:59 INFO: Done
The password for wazuh is Hhi7x3fbky53o3CUOqHrmmB_KYtrYPv2
The password for admin is essbe8HUvetLJIIiz8Dro7678KrJXq9L
The password for kibanaserver is pYrWmr_rp_9zwai6qIrVvbTVM0h0GFE1
The password for kibanaro is qf9yBeNk2jZmlf4jIIH0ju6EtsK7a7Sw
The password for logstash is ML1ORQzLFOhIfKzq28kbjMsaNs67Po0k
The password for readall is ByXXeu83_IDF4XonaGu_yKsHP98XCpKO
The password for snapshotrestore is CsMgHviug8DUJCqfWSe3yhc6_cKX0RXs
The password for wazuh_admin is kZ9t10NvDkursCQPPtYm1NkQRzoLjkYT
The password for wazuh_user is Zuc-cT34n1AD8I8Qd1AzfjAneytwwCdk
03/01/2022 07:28:59 INFO: Passwords changed. Remember to update the password in /etc/filebeat/filebeat.yml and /etc/kibana/kibana.yml if necessary and restart the services. More info: https://documentation.wazuh.com/current/user-manual/elasticsearch/elastic-tuning.html#change-users-password
03/01/2022 07:28:59 INFO: Checking the installation...
03/01/2022 07:29:00 INFO: Elasticsearch installation succeeded.
03/01/2022 07:29:00 INFO: Filebeat installation succeeded.
03/01/2022 07:29:00 INFO: Initializing Kibana (this may take a while)
.
03/01/2022 07:29:10 INFO: Installation finished
03/01/2022 07:29:10 INFO: You can access the web interface https://<kibana_ip>. The credentials are wazuh:Hhi7x3fbky53o3CUOqHrmmB_KYtrYPv2通过 https://
方法2:在CentOS 8 | RHEL 8 | AlmaLinux 8上逐步安装Wazuh服务器
我们要考虑的第二种安装方法是手动安装方法。您自己执行所有操作的地方。
在 CentOS 8|RHEL 8|AlmaLinux 8 上安装 Wazuh 服务器
确保您的系统已更新:
sudo dnf update -y
sudo dnf -y install vim curl unzip wget libcap添加 Wazuh GPG 密钥
sudo rpm --import https://packages.wazuh.com/key/GPG-KEY-WAZUH添加 Wazuh 存储库
sudo tee /etc/yum.repos.d/wazuh.repo <<EOF
[wazuh]
gpgcheck=1
gpgkey=https://packages.wazuh.com/key/GPG-KEY-WAZUH
enabled=1
name=EL-Wazuh
baseurl=https://packages.wazuh.com/4.x/yum/
protect=1
EOF安装 Wazuh 服务器:
sudo dnf -y install wazuh-manager运行 Wazuh 服务器
sudo systemctl enable --now wazuh-manager确认服务状态:
$ systemctl status wazuh-manager
● wazuh-manager.service - Wazuh manager
Loaded: loaded (/usr/lib/systemd/system/wazuh-manager.service; enabled; vendor preset: disabled)
Active: active (running) since Tue 2022-03-01 19:29:26 UTC; 2min 56s ago
Process: 15660 ExecStart=/usr/bin/env /var/ossec/bin/wazuh-control start (code=exited, status=0/SUCCESS)
Tasks: 117 (limit: 49281)
Memory: 139.5M
CGroup: /system.slice/wazuh-manager.service
├─15725 /var/ossec/framework/python/bin/python3 /var/ossec/api/scripts/wazuh-apid.py
├─15765 /var/ossec/bin/wazuh-authd
├─15782 /var/ossec/bin/wazuh-db
├─15806 /var/ossec/bin/wazuh-execd
├─15818 /var/ossec/bin/wazuh-analysisd
├─15880 /var/ossec/bin/wazuh-syscheckd
├─15893 /var/ossec/bin/wazuh-remoted
├─15926 /var/ossec/bin/wazuh-logcollector
├─15943 /var/ossec/bin/wazuh-monitord
└─15953 /var/ossec/bin/wazuh-modulesd
Mar 01 19:29:22 centos.example.com env[15660]: 2022/03/01 19:29:22 wazuh-syscheckd: INFO: (6678): No directory provided for syscheck to monitor.
Mar 01 19:29:22 centos.example.com env[15660]: 2022/03/01 19:29:22 wazuh-syscheckd: INFO: (6001): File integrity monitoring disabled.
Mar 01 19:29:22 centos.example.com env[15660]: 2022/03/01 19:29:22 rootcheck: INFO: Rootcheck disabled.
Mar 01 19:29:22 centos.example.com env[15660]: Started wazuh-syscheckd...
Mar 01 19:29:23 centos.example.com env[15660]: Started wazuh-remoted...
Mar 01 19:29:23 centos.example.com env[15660]: Started wazuh-logcollector...
Mar 01 19:29:23 centos.example.com env[15660]: Started wazuh-monitord...
Mar 01 19:29:24 centos.example.com env[15660]: Started wazuh-modulesd...
Mar 01 19:29:26 centos.example.com env[15660]: Completed.
Mar 01 19:29:26 centos.example.com systemd[1]: Started Wazuh manager.安装和配置 Elastic Stack
我们将继续安装 ELK 堆栈作为 Wazuh 服务器设置的一部分。 Elasticsearch、Filebeat 和 Kibana 组成了用于日志分析的 ELK 堆栈。这些工具与 Wazuh 服务器协作,提供安全事件分析和管理。
安装和配置 Elasticsearch
Open Distro for Elasticsearch 是 Elasticsearch 的开源发行版,Elasticsearch 是一种高度可扩展的全文搜索引擎。它提供高级安全性、警报、索引管理、深度性能分析以及其他一些附加功能。
运行以下命令来安装 Open Distro for Elasticsearch。
sudo dnf -y install opendistroforelasticsearch下载Elasticsearch的配置文件:
wget https://packages.wazuh.com/resources/4.2/open-distro/elasticsearch/7.x/elasticsearch_all_in_one.yml
sudo mv elasticsearch_all_in_one.yml /etc/elasticsearch/elasticsearch.yml 创建设置所需的用户和角色
for i in roles.yml roles_mapping.yml internal_users.yml; do
wget https://packages.wazuh.com/resources/4.2/open-distro/elasticsearch/roles/$i
sudo mv $i /usr/share/elasticsearch/plugins/opendistro_security/securityconfig/
done通过运行上述命令在 Kibana 中添加的 Wazuh 用户是:
Kibana 中添加了 Wazuh 附加角色,为用户授予适当的权限:
创建 SSL 证书
删除安装过程中生成的演示证书。
sudo rm -f /etc/elasticsearch/{esnode-key.pem,esnode.pem,kirk-key.pem,kirk.pem,root-ca.pem}下载用于生成所需证书的 wazuh-cert-tool.sh 脚本
sudo su -
curl -so ~/wazuh-cert-tool.sh https://packages.wazuh.com/resources/4.2/open-distro/tools/certificate-utility/wazuh-cert-tool.sh
curl -so ~/instances.yml https://packages.wazuh.com/resources/4.2/open-distro/tools/certificate-utility/instances_aio.yml以 root 用户身份执行脚本以创建所需的证书。
# bash ~/wazuh-cert-tool.sh
03/01/2022 20:55:51 INFO: Configuration file found. Creating certificates...
03/01/2022 20:55:51 INFO: Creating the Elasticsearch certificates...
03/01/2022 20:55:51 INFO: Creating Wazuh server certificates...
03/01/2022 20:55:52 INFO: Creating Kibana certificate...
03/01/2022 20:55:52 INFO: Certificates creation finished. They can be found in ~/certs.将 Elasticsearch 证书移动到相应位置:
mkdir /etc/elasticsearch/certs/
mv ~/certs/elasticsearch* /etc/elasticsearch/certs/
mv ~/certs/admin* /etc/elasticsearch/certs/
cp ~/certs/root-ca* /etc/elasticsearch/certs/运行以下命令以缓解 Apache Log4j2 远程代码执行 (RCE) 漏洞 – CVE-2021-44228 – ESA-2021-31:
mkdir -p /etc/elasticsearch/jvm.options.d
echo '-Dlog4j2.formatMsgNoLookups=true' > /etc/elasticsearch/jvm.options.d/disabledlog4j.options
chmod 2750 /etc/elasticsearch/jvm.options.d/disabledlog4j.options
chown root:elasticsearch /etc/elasticsearch/jvm.options.d/disabledlog4j.options启动elasticsearch服务并启用在系统启动时自动启动。
sudo systemctl enable --now elasticsearch确认状态以确认其正在运行:
$ systemctl status elasticsearch
● elasticsearch.service - Elasticsearch
Loaded: loaded (/usr/lib/systemd/system/elasticsearch.service; enabled; vendor preset: disabled)
Active: active (running) since Tue 2022-03-01 20:58:08 UTC; 1min 23s ago
Docs: https://www.elastic.co
Main PID: 16923 (java)
Tasks: 50 (limit: 49281)
Memory: 1.2G
CGroup: /system.slice/elasticsearch.service
└─16923 /usr/share/elasticsearch/jdk/bin/java -Xshare:auto -Des.networkaddress.cache.ttl=60 -Des.networkaddress.cache.negative.ttl=10 -XX:+AlwaysPreTouch -Xss1m -Djava.awt.headless=true >
Mar 01 20:57:51 centos.example.com systemd[1]: Starting Elasticsearch...
Mar 01 20:58:08 centos.example.com systemd[1]: Started Elasticsearch.运行 Elasticsearch securityadmin 脚本以加载新证书信息并启动集群:
export JAVA_HOME=/usr/share/elasticsearch/jdk/ && /usr/share/elasticsearch/plugins/opendistro_security/tools/securityadmin.sh -cd /usr/share/elasticsearch/plugins/opendistro_security/securityconfig/ -nhnv -cacert /etc/elasticsearch/certs/root-ca.pem -cert /etc/elasticsearch/certs/admin.pem -key /etc/elasticsearch/certs/admin-key.pem验证安装是否成功
# curl -XGET https://localhost:9200 -u admin:admin -k
{
"name" : "node-1",
"cluster_name" : "elasticsearch",
"cluster_uuid" : "n9h8pkMPTuW4r5R24YYdUg",
"version" : {
"number" : "7.10.2",
"build_flavor" : "oss",
"build_type" : "rpm",
"build_hash" : "747e1cc71def077253878a59143c1f785afa92b9",
"build_date" : "2021-01-13T00:42:12.435326Z",
"build_snapshot" : false,
"lucene_version" : "8.7.0",
"minimum_wire_compatibility_version" : "6.8.0",
"minimum_index_compatibility_version" : "6.0.0-beta1"
},
"tagline" : "You Know, for Search"
}安装和配置 Kibana 可视化工具
通过在终端中运行以下命令来安装 Kibana。
sudo dnf -y install opendistroforelasticsearch-kibana下载 Kibana 配置
wget https://packages.wazuh.com/resources/4.2/open-distro/kibana/7.x/kibana_all_in_one.yml
sudo mv kibana_all_in_one.yml /etc/kibana/kibana.yml 创建 Kibana 数据目录并设置正确的所有权权限。
mkdir /usr/share/kibana/data
chown -R kibana:kibana /usr/share/kibana/data下载 Wazuh Kibana 插件
cd /usr/share/kibana
sudo -u kibana /usr/share/kibana/bin/kibana-plugin install https://packages.wazuh.com/4.x/ui/kibana/wazuh_kibana-4.2.5_7.10.2-1.zip安装输出:
Transferring 33111704 bytes....................
Transfer complete
Retrieving metadata from plugin archive
Extracting plugin archive
Extraction complete
Plugin installation complete将 Elasticsearch 证书复制到 /etc/kibana/certs 中:
mkdir /etc/kibana/certs
cp ~/certs/root-ca.pem /etc/kibana/certs/
mv ~/certs/kibana* /etc/kibana/certs/
chown kibana:kibana /etc/kibana/certs/*将 Kibana 套接字链接到特权端口 443:
setcap 'cap_net_bind_service=+ep' /usr/share/kibana/node/bin/node启动并启用 kibana 服务:
systemctl daemon-reload
systemctl enable --now kibana该服务现在应该处于运行状态:
$ systemctl status kibana
● kibana.service - Kibana
Loaded: loaded (/etc/systemd/system/kibana.service; enabled; vendor preset: disabled)
Active: active (running) since Tue 2022-03-01 21:08:55 UTC; 7s ago
Main PID: 17578 (node)
Tasks: 11 (limit: 49281)
Memory: 167.6M
CGroup: /system.slice/kibana.service
└─17578 /usr/share/kibana/bin/../node/bin/node /usr/share/kibana/bin/../src/cli/dist -c /etc/kibana/kibana.yml
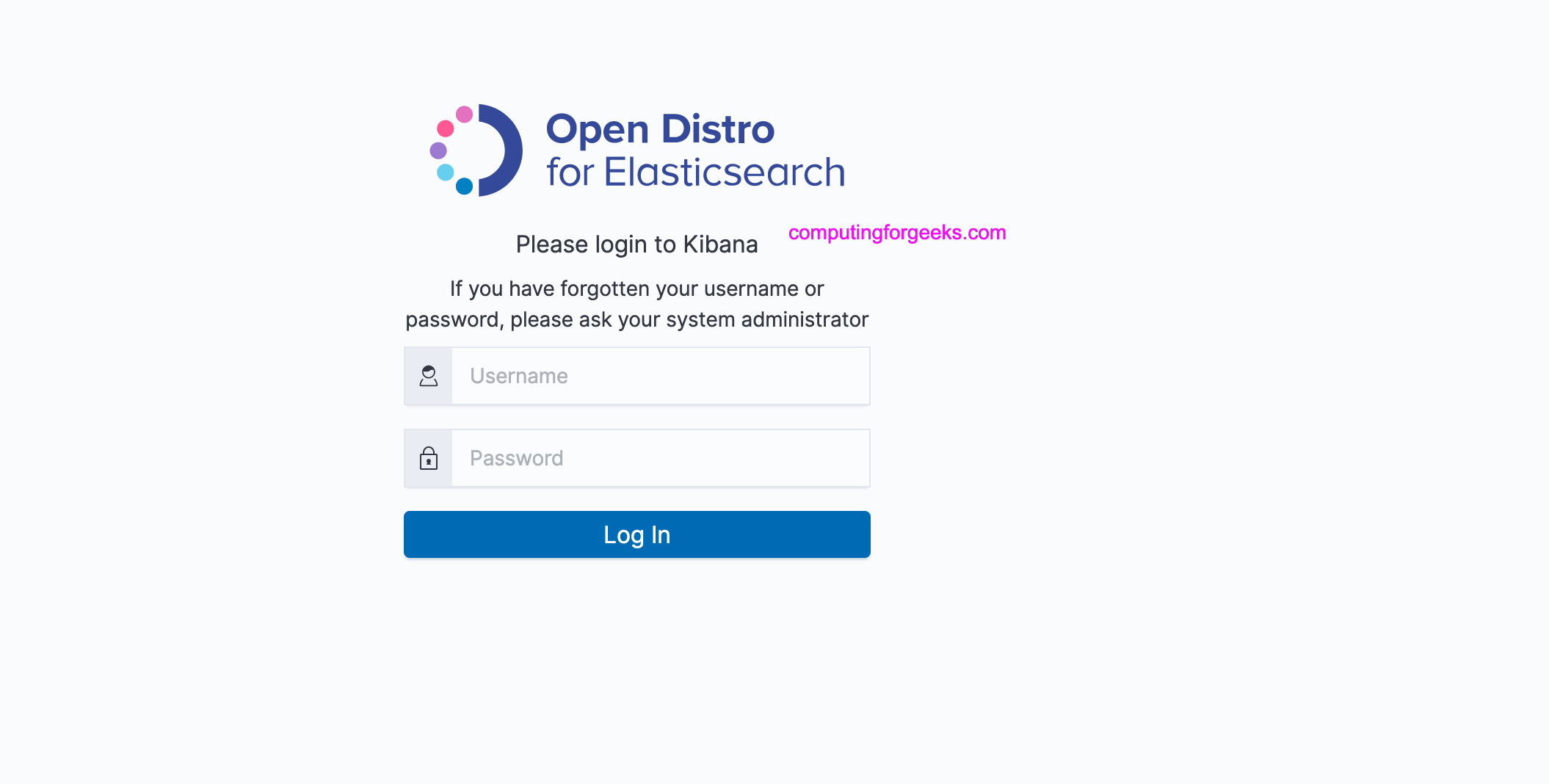
Mar 01 21:08:55 centos.hirebestengineers.com systemd[1]: Started Kibana.访问 Kibana Web 控制台:
URL: https://<wazuh_server_ip>
user: admin
password: admin安装和配置 Filebeat
Filebeat 是一个日志传送器,用于将日志从指定的日志目录传送到 Easticsearch。
sudo dnf install filebeat -y配置 Flebeat 以与 Wazuh 配合使用。备份现有的 Filebeat 配置文件,然后将其替换为下载的预配置文件。
wget https://packages.wazuh.com/resources/4.2/open-distro/filebeat/7.x/filebeat_all_in_one.yml
sudo mv filebeat_all_in_one.yml /etc/filebeat/filebeat.yml 下载 Elasticsearch 的警报模板:
wget https://raw.githubusercontent.com/wazuh/wazuh/4.2/extensions/elasticsearch/7.x/wazuh-template.json
sudo mv wazuh-template.json /etc/filebeat/wazuh-template.json
sudo chmod go+r /etc/filebeat/wazuh-template.json下载 Filebeat 的 Wazuh 模块:
curl -s https://packages.wazuh.com/4.x/filebeat/wazuh-filebeat-0.1.tar.gz | tar -xvz -C /usr/share/filebeat/module将 Elasticsearch 证书复制到 /etc/filebeat/certs 中:
mkdir /etc/filebeat/certs
cp ~/certs/root-ca.pem /etc/filebeat/certs/
mv ~/certs/filebeat* /etc/filebeat/certs/启用并启动Filebeat服务:
systemctl daemon-reload
systemctl enable --now filebeat
systemctl status filebeat确认filebeat安装成功。
# filebeat test output
elasticsearch: https://127.0.0.1:9200...
parse url... OK
connection...
parse host... OK
dns lookup... OK
addresses: 127.0.0.1
dial up... OK
TLS...
security: server's certificate chain verification is enabled
handshake... OK
TLS version: TLSv1.3
dial up... OK
talk to server... OK
version: 7.10.2通过 https://serverip_or_hostname 访问 Wazuh 服务器 Web 控制台
这样,您将能够通过在客户端系统上配置代理来使用 Wazuh 服务器监视您的系统。
查看此网站上的其他有趣文章:
- 使用 Beats 将服务器日志和指标转发到 Elasticsearch
- 在 CentOS 上使用 Icinga Director 自动化 Icinga2 配置 | RHEL 8
- 如何使用 Helm 在 Kubernetes 上安装 Netdata